
Data Protection Day
Data Protection Day, also known as Data Privacy Day, is an annual event observed on January 28th to raise awareness about the importance of privacy and the responsible handling of personal data. In an era dominated by digital interactions, safeguarding our sensitive information has become a critical aspect of our daily lives.
In an age where technology plays a central role in our personal and professional lives, Data Protection Day serves as a reminder of the need for robust measures to ensure the security and privacy of our data. The day emphasizes the significance of creating a culture of responsible data management, not just for individuals but also for businesses and organisations.

Data Protection Day encourages a shift in mindset towards making privacy a fundamental consideration in the development and deployment of technology. Whether it's the creation of new applications, the handling of customer data, or the implementation of internal processes, prioritising privacy should be integral to all aspects of our organisation.
As technology continues to evolve, so do the challenges associated with data protection. Therefore, ongoing education and awareness initiatives are vital, aimed at educating colleagues about the latest threats, best practices, and emerging technologies in the realm of data protection.
Data Protection Day serves as a timely reminder to reflect on the importance of privacy in our digital age. By embracing responsible data management practices, individuals, businesses, and organisations can contribute to creating a safer and more secure digital environment for everyone.

Individuals are encouraged to take proactive steps in safeguarding their personal information. This includes being cautious about the information shared online, using strong and unique passwords, making use of additional security measures such as two-factor authentication, and staying informed about privacy settings on various platforms. Data Protection Day serves as an opportunity for everyone to assess and enhance their digital security practices.
For organisations, Data Protection Day serves as a call to action to prioritise data privacy. With a global increase in the number of data breaches and cyber threats, organisations must implement robust security measures, conduct regular audits, and educate employees about the importance of data protection. Compliance with data protection regulations, such as the General Data Protection Regulation (GDPR), is also crucial in maintaining trust and avoiding legal repercussions and enforcement actions.

Benefits of Generative AI
Efficiency and Productivity: Generative AI platforms have proven invaluable across industries, streamlining tasks and accelerating processes. The capability to rapidly generate content, from images to code snippets, contributes significantly to time efficiency.
Personalisation and Customisation: Analysing extensive datasets enables Generative AI to create personalised experiences for users. This ranges from tailored content to customised designs, enhancing user engagement and satisfaction.

Navigating GDPR Compliance
Documentation and Transparency: To align with data privacy regulations, it’s imperative that organisations produce documentation and guidance to communicate what responsible usage of Generative AI does and doesn’t look like.
Limit The Use of Personal Data: Avoid at all costs using client/company private, confidential or restricted data within the Generative AI input prompts. In short, if the information is not in the public domain, don’t enter it into the AI tool. Furthermore, under no circumstances should the input prompts contain personal data about individuals (e.g. company email addresses, names etc.).
Fairness and Inclusivity: Mitigating biases in AI-generated content is crucial for ensuring fairness and inclusivity. This aligns with our privacy legislative framework’s commitment to non-discriminatory and just data processing practices. Consider for example how automated solutions may be used to pre-filter/pre-categorise data, and how any biases might affect the outcomes.

Generative AI: Understanding Benefits and Privacy Challenges
In the realm of workplace technology, Generative AI has emerged as a powerful tool, offering efficiency and potential innovation. Generative AI tools operate by employing advanced machine learning techniques which are trained on massive datasets to understand patterns and underlying structures within the data. The models learn to create new instances of data that mirror the training data and are designed to resemble human output. As we explore the potential applications of such models, it's crucial to understand both the advantages it brings and the potential privacy challenges, particularly concerning GDPR and individual rights.

Privacy Challenges
Data Memorisation: Generative AI models, if not carefully managed, may inadvertently retain sensitive information from training datasets. This memorisation poses a risk to privacy, as the models may generate content that compromises personal details.
Biases in Output: The inherent biases present in training data can influence the content generated by AI models. Unchecked, this can lead to biased or unfair content, raising concerns about ethical considerations and GDPR compliance.
Lack of Transparency: The algorithms used in AI systems can be complex, and it can be difficult for individuals to understand how their data is being used to create content that could affect them. This data can be obtained from a variety of sources including the users’ online activity, social media posts and public records. These can reveal a lot about a person’s life, including their ethnicity, religion and political beliefs.

Balancing Benefits and Risks
Striking a balance between leveraging the benefits of Generative AI and mitigating associated risks requires a cautious approach. Here's a practical guide:
Regular Auditing: If you are managing a team which uses Generative AI models from time to time, you should conduct regular audits to monitor the outputs of the models, ensuring that privacy considerations are actively addressed.
Cultivate Responsible Practices: Foster a workplace culture that values responsible and ethical use of Generative AI within your teams. This includes prioritising privacy considerations as an integral part of the innovation process by liaising with the Privacy & Compliance team to ensure a balanced and ethical approach to Generative AI utilisation.
In conclusion, Generative AI may offer substantial benefits for workplace productivity and innovation. As we navigate the integration of Generative AI tools into our workflows, it is essential that we approach this technological advancement with a keen awareness of the inherent privacy risks. By adopting responsible practices, ensuring adequate governance, and addressing transparency concerns, we not only uphold regulatory standards but also cultivate a workplace culture that prioritises responsible and ethical data usage within Generative AI applications.
Security Incident Reporting: How you can make a difference
According to an analysis by IT Governance, a leading provider of cyber risk and privacy management solutions, more than 8 billion records were breached in 2023 – and this is only based on breaches that were reported publicly!
Data breaches and cyber attacks continue to present huge risks to businesses and individuals. Many breaches are the result of intentional, financially-motivated attacks, but even accidental or inadvertent breaches affecting limited numbers of records can result in harm to CPM, our employees, our clients or their customers.

While you might be tempted to first make contact with a member of the Privacy & Compliance team more informally by email or Teams chat, it's important to email CPMIncidents@cpm-int.com first instead. The P&C team receives the incident emails, but there are many issues that Omnicom's security team needs to help us with, so this makes sure they are notified as well.
Even if you are not sure whether to report something, please do so – we'll help you work through the details, and we'd rather incidents be overreported than underreported.


One of the most important ways you can make a difference is by immediately reporting actual or suspected security incidents to CPMIncidents@cpm-int.com. This ensures that the right people in CPM's Privacy & Compliance team, as well as Omnicom's Security Operations Center, are notified and can step in to begin the investigation and containment of any incident. Seconds, minutes and days can make all the difference, so the sooner we know about an incident, the sooner we can ensure we fulfil our contractual and legal requirements, and more importantly, maintain the trust of our clients and our employees.

Confused about what a security incident is? Not sure when you should report something? Let´s take a closer look.
- What is a Security Incident? A Security Incident is a single event or series of events that indicates that the security of information or an information system, service or network may have been or was breached or compromised.
- What is a Personal Data Breach? A Personal Data Breach is an unauthorized destruction, loss, alteration, disclosure of or access to data. A Personal Data Breach is a type of Security Incident. All Personal Data Breaches are Security Incidents, but not all Security Incidents are Personal Data Breaches. Quick identification and remediation of a Security Incident may stop a Personal Data Breach from occurring.
- So, what should I report? In short, anything that makes you suspect a Security Incident may have occurred, whether this could involve Personal Data or not. This can be anything from a misdirected email containing personal data sent to an unauthorized person, to a ransomware attack, and anything in between.
- What about phishing emails, are those Security Incidents?
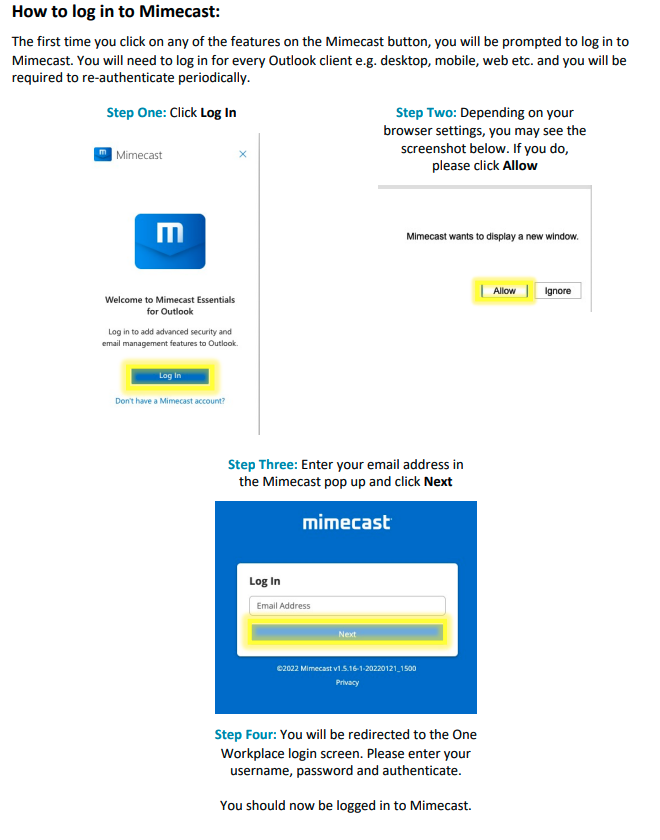
- No, if all that's happened is that you received an email. Simply receiving a phishing email is not a Security Incident, though you should immediately report that using the “Report Message” button in Outlook. (See this newsletter for more instructions about how to spot and avoid phishing attacks, and logging into Mimecast).
- If, however, if you took any action on the phishing email – replied to it with confidential information, clicked on a link, or opened an attachment for example – then you must report this as a Security Incident, so that the team can investigate and if needed take action to prevent or limit the extent of the damage.

The Risks of Oversharing
Social Engineering Attacks: Sharing detailed work information provides cybercriminals with valuable insights for social engineering attacks. From seemingly harmless details like job titles and colleagues' names to more sensitive information like project details or upcoming events, cyber attackers can exploit these nuggets to craft convincing scams or impersonate colleagues.
Phishing Vulnerabilities: The information shared on social media often becomes fodder for phishing attempts. Cybercriminals may use the details posted by employees to craft personalised phishing emails or messages, tricking individuals into revealing sensitive information or clicking on malicious links. The more details available, the more convincing these phishing attempts can become.
Reputational Damage: Oversharing work-related content can have reputational consequences. Posting about internal matters, complaints, or confidential projects can harm not only the individual but also the organisation's image. This may lead to strained professional relationships, damage to career prospects, and even potential legal consequences. Please consider that some clients insert clauses into their contracts with us that prevent us from disclosing publicly that we work with them.

Best Practices for Social Media Use
Think Before You Share: Before posting work-related details, pause and consider the potential implications. Ask yourself whether the information is suitable for public consumption and whether it could be exploited by malicious actors.
Adjust Privacy Settings: Leverage the privacy settings on social media platforms to control who can view your posts. Restricting access to a more limited audience minimises the risk of unauthorised individuals accessing sensitive information.
Avoid Sharing Confidential Details: Steer clear of sharing confidential project details, internal discussions, or any information that could compromise information security. This not only protects individuals’ privacy but also upholds the organisation's commitment to confidentiality.

Social Media: A commitment to privacy when sharing
In an age where social media is an integral part of our personal and professional lives, exercising caution in sharing work-related details is paramount. This is not merely about maintaining a boundary between personal and professional spheres; it's a crucial step in safeguarding individual privacy and protecting against the risks of social engineering and phishing. Let's delve into why employees should be mindful of what they share and explore the GDPR and privacy considerations associated with social media use.

GDPR and Privacy Considerations
Employee Consent and Control: The GDPR emphasises the importance of individual consent and control over personal data. You should take special care with the information you share on social media, especially if it pertains to work colleagues and could be considered their personal data. It is essential for us all to remain vigilant and aware about the implications of sharing such information.
Data Minimisation: The GDPR promotes the principle of data minimisation, this means collecting only the data necessary for the intended purpose. Employees should be mindful of this principle when, not only sharing work-related information on social media, but using social media to collect information about others. Invasive data processing practices increase the risk of privacy breaches and the potential for misuse of information.
Purpose Limitation: Understanding the purpose of sharing and collecting information is crucial. If the purpose is purely personal and unrelated to work, employees should exercise caution in not attempting to conflate personal and professional uses of the data.

Stay Informed: Regularly review and understand the privacy settings of the social media platforms you use. These settings often evolve, and staying informed helps you maintain control over your online presence.
In conclusion, you play a pivotal role in safeguarding your own privacy and that of the business by exercising caution in your use of social media. With data privacy principles reinforcing the importance of consent, data minimisation, and purpose limitation, each one of us should be proactive in understanding and applying these principles to our online activities. By adopting a thoughtful and mindful approach to your social media use, you contribute to a secure digital environment for each of us as individuals, and for the business in general.
