
Trending toward trust
The global data privacy and compliance landscape has continued to evolve over the almost 5 years since GDPR came into force with the focus on data protection legislation intensifying across all major geographies. 157 out of a possible 194 countries have now put in place legislation to secure the protection of data and privacy, and new laws continue to be introduced as regulators attempt to keep pace with the emergence of data-sharing technologies globally.

In summary, organisations that can actively demonstrate that they are responsible and trustworthy custodians of data are probably more likely to reap the benefits, and importantly, the customers to realise their future growth. Our business is uniquely positioned to access the in-house expertise of a Privacy & Compliance Team which can support in the development and delivery of innovative solutions for our clients.
If you have any questions in relation to our privacy and compliance programmes, please reach out to your local in-market Data Protection Champion (details on the CPM Privacy & Compliance SharePoint Site) or email Privacy@cpm-int.com.

Talking about laws and regulations can sometimes feel like there is an emphasis on inhibiting creativity, however, this provides our business an incredible opportunity to continue trending towards trust.
Trust is fundamentally built upon two core concepts – transparency and accountability. We demonstrate both competence and integrity by focussing on delivering on these two data privacy concepts, thus enhancing our reputation and deepening our relationships with our clients.
The commercialisation of data-centric activities and the proliferation of ancillary technologies are increasingly important in businesses like our own, thus data literacy across all levels of the organisation is mission critical to our operations.


CPM's ISO 27001 journey
Over the past year, CPM have been on a journey with Omnicom to fully align our information security practices to the ISO 27001 standard for information security. The ISO 27001 Information Security Management System (ISMS) is the leading international standard focused on information security. The standard provides requirements and guidance on the development and implementation of a best-in-class ISMS. CPM Spain is already ISO 27001 certified (since 2021) and so the ISO 27001 journey was not new to CPM. As a result of the Omnicom ISO 27001 programme, a number of new/updated Omnicom Policy and CPM Procedure documents are now available.
Updated Omnicom Policies can be accessed via the Omnicom IT Central SharePoint site and updated CPM Procedure documents can be accessed via the CPM Privacy & Compliance SharePoint Site.
As we continue on our ISO 27001 journey, more information will be shared through future editions of this newsletter and via targeted communications.
Phishing & Ransomware
We are all aware of the increasing threats of cyberattacks to businesses today. Among these threats, phishing and ransomware are two of the most common and destructive. As such, it is important to understand how these attacks can affect us personally and professionally.
Phishing is an attack that relies on tricking individuals into giving away sensitive information, such as passwords or financial data, through emails, text messages, or fake websites that appear to be trustworthy. Falling for a phishing attack can result in the theft of sensitive information, leading to financial fraud and identity theft.
On the other hand, ransomware is a type of malware that can encrypt a victim's files, rendering them inaccessible. The attacker then demands a ransom payment in exchange for the decryption key, which can be disruptive to business operations.
The consequences of falling for these attacks can be devastating for businesses and it is therefore crucial that we understand how to recognise these threats and take the necessary measures to protect ourselves and our business.

To protect against ransomware, you should take the following steps:
- Regularly backup important data and store the backup in a designated SharePoint folder or secure Teams site
- Restart your laptop regularly to help keep all software and security systems up to date
- Be cautious of email attachments, especially those from unknown senders or that have unexpected extensions, like .exe or .zip
It's also important for businesses to have a response plan in place in case they fall victim to a phishing or ransomware attack. This plan should include steps for notifying employees, customers, and relevant authorities, as well as steps for mitigating the damage and restoring normal operations.
To this end, we are currently involved in an ongoing process to update and implement a robust Business Continuity Management Plan, and will provide more information about this in due course.
By remaining vigilant and taking these simple steps, you can help us protect sensitive information and critical business data, and reduce the risk of falling victim to a ransomware attack.

Some tips to avoid phishing attacks include:
- Being cautious of unsolicited emails or messages, especially those that ask for personal or sensitive information
- Checking the sender's email address and website URL before clicking on any links or downloading attachments
- Avoid entering sensitive information into websites unless you are certain that the site is legitimate
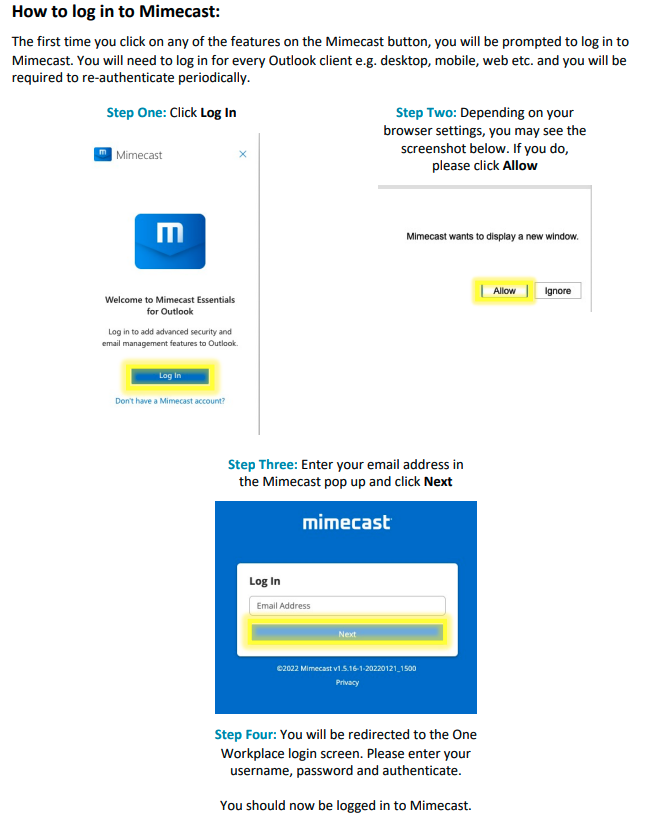
- Use the "Report Message" button in outlook for any suspicious emails you receive (Note: You will need to log in to Mimecast the first time you click on the button.)

Are you up to date with training?
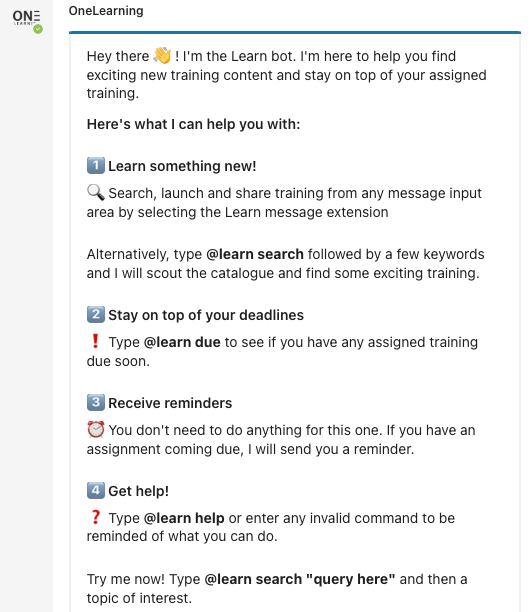
Omnicom's new “OneLearning” platform launched in January, bringing with it a range of improved features and a number of optional and mandatory training modules. You can check if you have any mandatory modules outstanding by accessing OneLearning from the Omnicom OneWorkplace page, by clicking on the OneLearning tile.
Omnicom have also recently launched a OneLearning Teams app where you can search for and share training as well as receive notifications about training with upcoming and outstanding due dates. All links to training in the app will take you directly to the learning details page.
The app is available in local language, based on your language selection in Teams. The language does need to be one of the languages supported in OneLearning; if it is not supported results will be returned in English.
The image to the left shows some of the useful features available via the app.
Why is it important to lock unattended devices?
We all know how important it is to protect sensitive company data and maintain the confidentiality of our work. One of the most basic ways to achieve this is to ensure that our computers, tablets, mobile devices, and other paper documentation are locked and secured when we step away from our desks, even if it's just for a few minutes.

Secondly, each of us – whether to a lesser or a greater extent – has access to confidential client information, intellectual property, financial data, personal data and more via our company-issued devices. Our use and access to much of this kind of data is subject to various regulations (e.g. the GDPR) and must be treated accordingly. A single data breach could lead to serious consequences, including financial losses, reputational damage, and legal action.
Lastly, it’s just good practice. Integrity is a key component upon which trust is predicated. Each of us being able to consistently demonstrate good stewardship of the data we are entrusted with reinforces to our clients, visitors and colleagues that we are invested in supporting the organisation’s information security programme. Employees who are full participants in protecting company data are crucial to us obtaining and maintaining accreditations such as ISO 27001, and affirms to current and prospective clients that we can be trusted partners.
By following the steps detailed, you can help protect our company's sensitive information and ensure that we're meeting compliance requirements.
Let's all do our part to maintain a secure work environment.
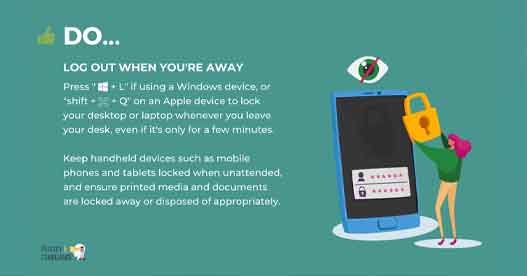
Why is this so important? First and foremost, it’s what our clients expect of us. Almost all of our clients include clauses in their contracts with us requiring their data to be segregated and or made available only on a strictly need-to-know basis. This means that only the teams and individuals directly involved in the delivery of work against that specific contract, should ever be able to access the client data obtained or produced under that contract. Regardless of how trustworthy our colleagues are, leaving computers and documentation accessible to others when unattended undermines the organisation’s ability to meet these client requirements.
-1.png)

Updated guidance for managing supplier relationships
We've recently produced an updated procedure for managing supplier relationships which is available on the CPM Privacy & Compliance SharePoint Site.
The procedure is specifically aimed at supporting the selection, engagement and managmeent of suppliers by CPM where:
- The supplier provides critical services or products to CPM; or
- The supplier will be accessing or otherwise processing CPM, Omnicom, and/or Client confidential data, including but not limited to personal data.
The principles detailed in and tools provided alongside the procedure can however be used for all types of supplier engagements. Questions about whether or how the procedure applies can be directed to privacy@cpm-int.com
We're looking for your feedback!
We're keen to hear your ideas for content for future editions of the CPM Privacy & Compliance newsletter so that we can ensure that we're covering the topics and themes that are important to you and ultimately to our business and that of our clients. Please share any ideas that you may have on our anonymous feedback form.

